 OpenSouls·34w
OpenSouls·34wUUIDv47
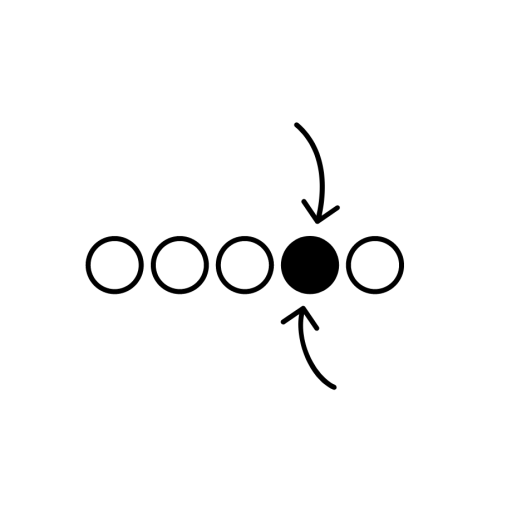
UUIDv47 is a library that enables reversible transformation between UUIDv7 (time-ordered) and UUIDv4 (random-appearing) formats. It allows developers to hide time-ordering from external APIs while maintaining internal chronological benefits, using cryptographically secure SipHash-2-4 algorithm with high performance and zero dependencies.





