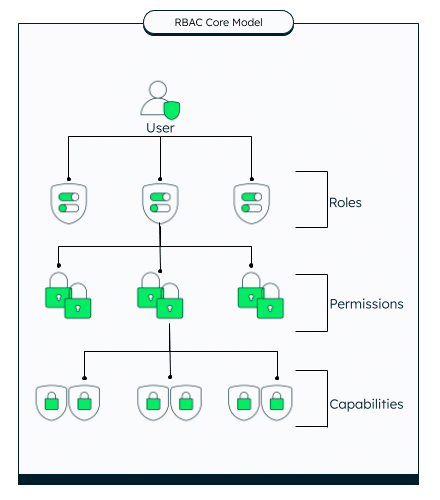
Authentication alone is insufficient for secure Java applications — authorization must also be modeled explicitly as business logic. This walkthrough demonstrates implementing RBAC in Java by defining permissions as enums, grouping them into roles, storing user metadata in MongoDB, and centralizing authorization in a dedicated
Sort: