Each JWT is additionally signed using cryptography (hashing) to ensure that the contents of the JWT cannot be changed by the client or an unsavory party. The JWT will be delivered as a parameter or authorization header from the user agent whenever the user tries to access a protected resource, such as an API or a protected route.
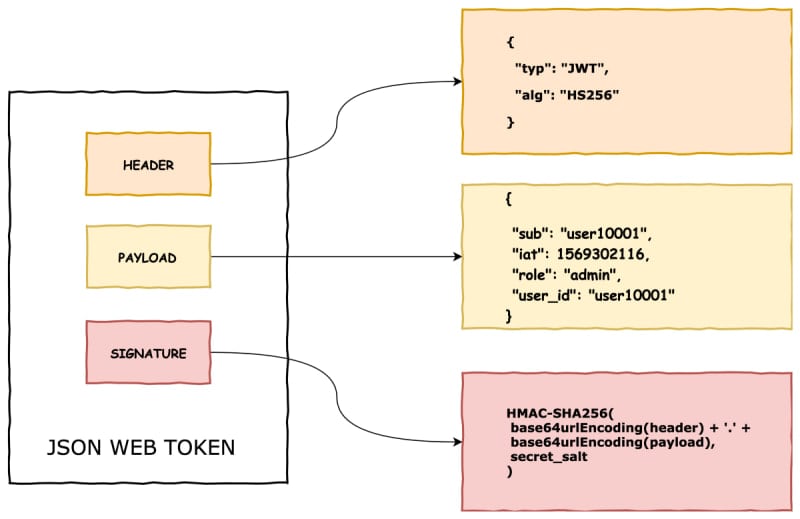
Table of contents
JSON Web TokensIntroductionTokensJSON Web Tokens StructureHow is signature is used to ensure AuthenticationWhere to Store JSON Web TokensWhat If I Want to Encrypt My Tokens Anyway?How do JSON Web Tokens work?What are JSON WEB TOKENS used for?Steps to Create a JSON Web TokenSteps for Validating a JSON Web TokenAdvantages of JWTsDisadvantages of JWTsConclusion1 Comment
Sort: