Hacking JWT is most commonly used to identify an authenticated user. In most cases it is used as a “session token’s used in APIs but is used for all types of web apps. We will use a very good tool created to exploit many JWT attacks, I recommend it is very good. To exploit this vulnerability we are going to use a web platform lab called PortSwigger.
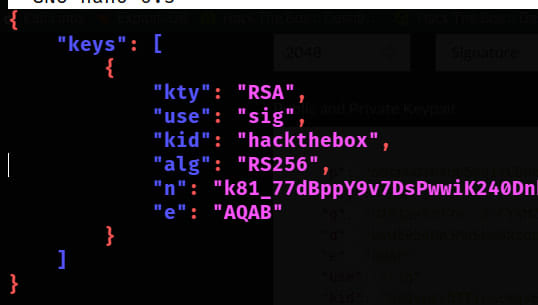
Table of contents
ExploitationNone AlgorithmWeak SecretKey ConfusionKID Parameter InjectionJKU Parameter InjectionConclusions3 Comments
Sort: